Since 2005, more than 320 state-sponsored cyber operations have been conducted. The ever-increasing rate of cyber operations has raised the prospects of cyber conflicts. With more than 30 states having the capability to conduct cyber-attacks, it is imperative to introduce measures to regulate the behaviour of states in the cyber domain. In this regard, cyber-peacekeeping has emerged as a potential measure to deal with the cyber dimension of current and future military conflicts. The article deals with the challenges confronting the creation of a cyber-peacekeeping force and also offers recommendations in the form of a general framework regarding the operationalization of such a force.
Generally, cyber-peacekeeping is analogous to physical peacekeeping with the distinction that cyber-peacekeepers are solely deployed for cyberspace alone. A review of existing scholarship on cyber-peacekeeping reveals at least 27 potential tasks for cyber-peacekeeping for cyber-peacekeepers which include the following:
- Monitoring for actions in cyberspace that violate peace agreements
- Monitoring human rights abuses occurring in cyberspace
- Creation of a cyber-buffer zone
- Disarmament of cyber weapons
- Demobilization of cyber combatants
- Prevention or warning of impending cyber-attacks
- Investigating cyber-attacks
- Mediating between conflicting parties through either ‘cyber ceasefires’ or by developing ‘cyber-peace agreements’ for ending cyber conflicts
Despite the emergence of the cyber-peacekeeping as a research area nearly two decades ago, nothing substantial has been materialized. This is due to numerous concerns, objections and criticisms which question the very idea of cyber-peacekeeping. In this regard, the four main challenges are as follows:
- Insufficient Capabilities and Expertise – The United Nations currently does not have sufficient capabilities and expertise to deploy such a force. To fill the existing gap, states can provide their capabilities, expertise and resources. However, it will be a challenge to convince states owing to their ‘national interests’ and a shortage of cyber experts at home.
- Redundant Measure – Some experts have opined that establishing a cyber-peacekeeping force will be a redundant measure and add to expenditures since existing peacekeeping mechanism include efforts to counter cyber-attacks through inter-government cooperation.
- No Clarity of Physical or Visible Battlefield – Contrary to physical territorial boundaries, there are no territorial boundaries in cyberspace. The non-existence of such boundaries has been a source of extensive debates among experts. However, some argue that it should not prevent the establishment of a cyber-peacekeeping force because the nature of cyber warfare is uncertain and not fully comprehended.
- Unavailability of Legal Framework – No proper mechanism currently exists which can decide which cyber-attacks are acts of war or otherwise. Moreover, several legal issues have been raised and will be raised in future regarding the conduct of cyber-peacekeeping force. However, the legal hurdles can be resolved through the relevant UN Security Council (UNSC) resolutions, specific operational mandates, etc.
If a cyber-operation is carried out as part of a peace operation below the threshold of armed conflict then human rights law will be applicable. The law of armed conflict will be applicable for peace operations if the threshold of armed conflict is crossed in addition to the applicability of human rights law.
From an international law perspective, it is prerogative of the UNSC to decide whether the cyber-operations amount to threatening international peace and security under Article 39 of the UN Charter. However, various legal instruments will be applicable depending on the context of cyber-operations. If a cyber-operation is carried out as part of a peace operation below the threshold of armed conflict then human rights law will be applicable. The law of armed conflict will be applicable for peace operations if the threshold of armed conflict is crossed in addition to the applicability of human rights law. In this regard, non-forceful measures stated in Article 41 of the UN Charter can be applied. However, determining which cyber-operation amounts to use of force or not depends on whether peace operation is a party to an armed conflict or not.
Table 1 – Conceptualizing deployment of cyber-peacekeeping force in various scenarios
(Kleffner & Dinniss, 2013)
| Scenario | Nature of Mandate | Modus Operandi |
| Peacekeepers deployed in a region marred by offensive cyber operations. | Any response mechanism will depend on the mandate of the peace operation. | Monitor and conduct cyber operations in response to cyber threats and monitor internet traffic. |
| Offensive cyber operations targeting UN peace operations. | Principles of necessity and proportionality / Just War Theory. | Use of all available means including the use of force for self-defence or defence of the mandate. |
| Offensive cyber operations targeting civilians in UN peace operation’s area of responsibility. | The mandate to protect civilians is expressed in terms of ‘to the extent possible’ and ‘within mission capabilities. | Use of force and technological means for the protection of civilians from the imminent threat of physical danger. Additionally, mechanism of persuasion and coercion can be used for mediation. |
| Peacekeepers employing offensive cyber operations against adversaries. | Any use of offensive cyber operation will depend on the mandate of the peace operation. | Use of offensive cyber operations. |
In terms of the prospects of establishing a cyber-peacekeeping force, the establishment of ‘Digital Blue Helmets (DBH)’ (analogous to blue helmet wearing physical UN peacekeepers) is viewed as an indicative factor showing how UN sees its future potential role in cyber-peacekeeping.
In terms of the prospects of establishing a cyber-peacekeeping force, the establishment of ‘Digital Blue Helmets (DBH)’ (analogous to blue helmet wearing physical UN peacekeepers) is viewed as an indicative factor showing how UN sees its future potential role in cyber-peacekeeping. DBH programme proposed a three-tier cybersecurity monitoring mechanism with the main ‘Global Cybersecurity Monitoring Centre’ located in New York in addition to regional and non-regional monitoring centres. Additionally, the UN is slowly developing the necessary cyber infrastructure and procedures to protect sensitive information pertaining to peace operations from break-ins.
Adding to the existing literature, a brief general framework is presented here regarding the operationalization of a future cyber-peacekeeping force. For formulating a working modus operandi, the UN can arrange various sessions or constitute a group of governmental experts in which government officials, tech companies, research institutes, think tanks, academia, etc. discuss the formation and modus operandi of such a force.
For building a cyber-peacekeeping force, the UN will rely on member states and tech companies to provide cyber experts whereas civilian cyber experts can volunteer their time in the form of civilian peacekeepers. Additionally, a dedicated full-time UN staff will be required for administration and coordination related tasks of the force.
The cyber-peacekeeping force can be embedded into the current hierarchical structure of UN peacekeeping by establishing a distinct cyber unit comprising cyber experts in the form of military, police and civilian peacekeepers.
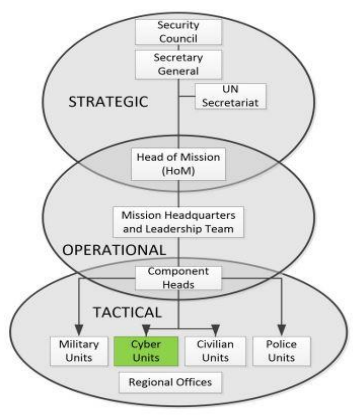
Figure 1 – Proposed UN Peacekeeping Organizational Structure (Robinson, Jones, Janicke & Maglaras, 2018)
For smooth operationalization of the unit, virtual collaborative environment, defined as digital spaces where remotely located people can come together and interact with each other and with virtual objects, can be adopted. Such an environment should:
- Cater to both small and large scale cyber-peacekeeping activities
- Accept concurrent users with no failures of availability
- Securely transmit sensitive information
- Contain resource sharing component, Voice over Internet Protocol and reporting system
In the coming years, cyber operations are likely to be directed at UN peace operations or used by peace-keeping operations in the implementation of their mandates. However, the creation of UN cyber-peacekeeping force might seem a far-sighted idea at this point. Instead, a cyber unit comprising cyber experts from troop-contributing countries, tech companies, think tanks, volunteers to UN peace operations, is likely to be utilized for both offensive and defensive cyber operations. Before the formulation of such a unit, it is important to address all the underlying legal hurdles regarding its conduct. Similarly, the jurisdiction of this unit should be mentioned in the peace operation’s mandate as authorized by UNSC so to not leave any chance of ambiguity. In addition to awareness initiatives, all major stakeholders should undertake efforts to formulate legal frameworks for ensuring cybersecurity.
